Most serious incidents aren't caused by one dramatic flaw. They're caused by two or three moderate ones that nobody connected.
Whole Enterprise Security Assessment
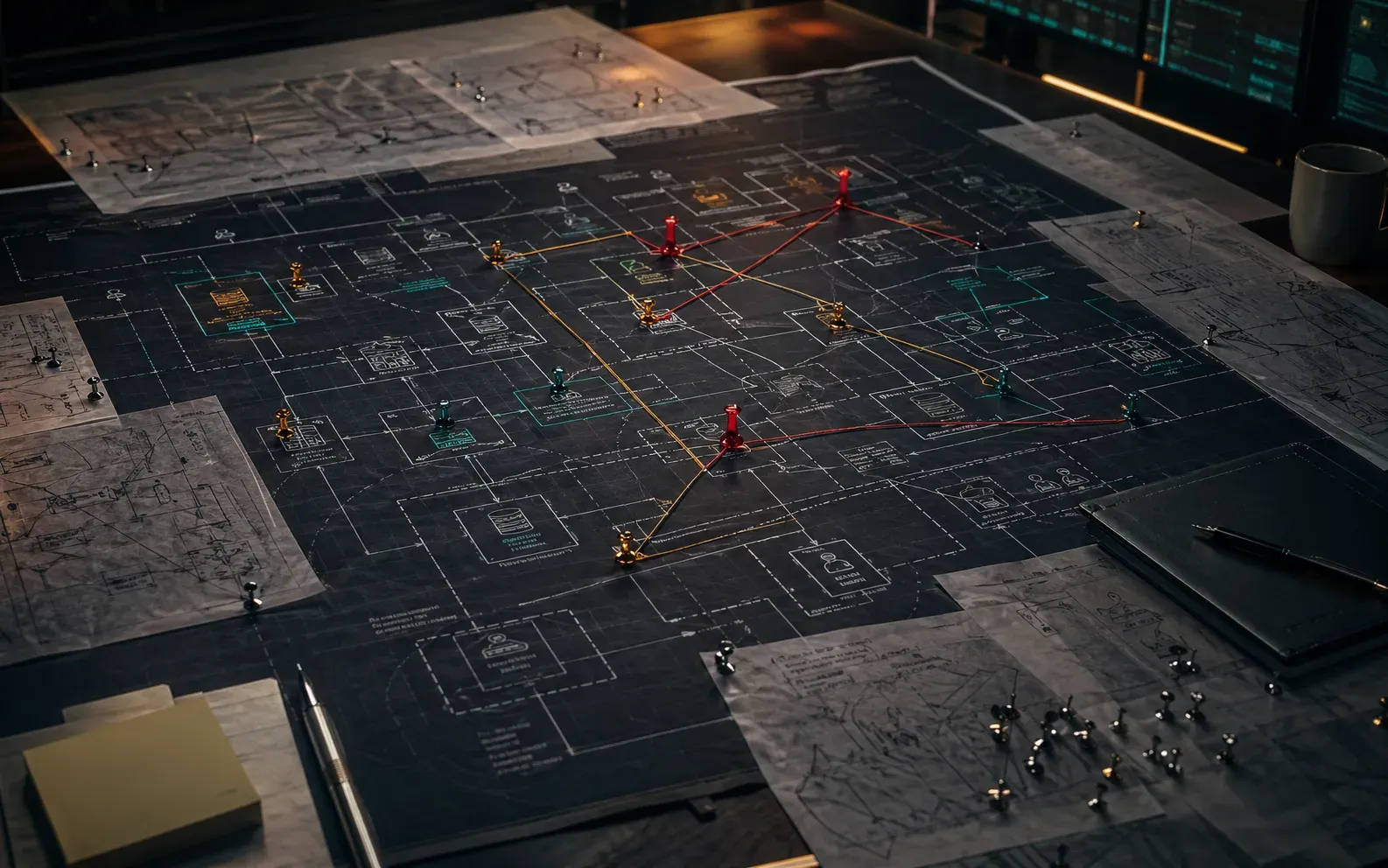
The breach that keeps you up at night isn't one big flaw. It's three small ones holding hands.
I perform enterprise-minded security reviews for companies that need the real picture, not a narrow point-in-time scan. We look across product, cloud, identity, engineering workflow, AI systems, and operational practices — because the vulnerabilities that compound together are the ones that hurt.
Best fit
Whole Enterprise Security Assessment
- Assessment report with prioritized findings and remediation themes
- Architecture-level risk review across critical systems
- Executive summary for leadership and detailed guidance for engineering
- Follow-up planning session to sequence the fixes
Coverage across app, cloud, identity, AI
Findings prioritized by business risk
Roadmap your team can execute
Why teams call
The pattern I keep seeing.
Fast-moving engineering orgs quietly accumulate risk in build pipelines, auth layers, cloud defaults, and AI integrations — none of it alarming in isolation.
Leadership needs a prioritized remediation plan, not a scanner report that reads like a legal filing.
What changes
What actually gets better.
Reveal the risk patterns connecting product, infrastructure, identity, AI, and developer workflow.
Prioritize findings by impact, exploitability, and business urgency rather than by generic scanner severity alone.
Separate what needs immediate remediation from what can be scheduled responsibly.
Give engineering leadership a roadmap they can defend to product, ops, and the executive team.
How I work
No mystery, no handoff decks.
Survey the attack surface
We examine the product, the cloud, the identity layer, developer tooling, and the new AI-specific surfaces that most classic reviews miss.
Connect the dots
I look for the combinations that turn several small issues into one expensive incident path.
Turn findings into decisions
You get a practical remediation plan with owners, priorities, and tradeoffs instead of a report that dies in a folder.
Next step
Ready to stop circling it?
Bring whatever your team keeps putting off — the scary migration, the expensive AI bill, the app that misbehaves in production. We'll figure out what's actually blocking it.